Welcome
Welcome
Hello and Welcome!
Be sure to attend our monthly meetings. Lots of good information there. Register for our Thursday April 30th Virtual Meeting on our site ISC2CT.org
Also come Join our (ISC)2 Connecticut Chapter Discord Server
Upcoming events:
ISC2 Spotlight Event on Cloud Security | April 22-23 | Virtual Event 5.5 CPEs Free to Attend Join your fellow ISC2 members, associates and candidates for an exclusive ISC2 Spotlight on Cloud Security where top industry experts will cover the latest cloud adoption strategies, tackle emerging threats and attack vectors, explore cutting-edge security practices and provide actionable insights to safeguard your cloud environments.Registration
SANS AI Cybersecurity Summit 2026 | Mon, April 20-21 | Live Virtual Summit CPEs: 8 Free to Attend The AI Cybersecurity Summit brings together the most critical aspects of AI in cybersecurity. From leveraging AI to strengthen your defenses to protecting against sophisticated AI-powered attacks that are already reshaping the threat landscape.Schedule & Registration
Upcoming Training:
NII Certified AI Security Practitioner v2.0 (CAISP v2.0) Training Workshop | April 21-23 Online 16 CPE Credits | USD 199 Regular participant USD 129 ISC2 members We’re excited to announce our upcoming updated program, Certified AI Security Practitioner v2.0 (CAISP v2.0) training, a deep dive into AI/ML cybersecurity with enhanced focus on LLMs, secure MLOps, and emerging AI risks. Certified AI Security Practitioner v2.0 (CAISP v2.0) training, builds on the foundation by diving deeper into technical, practical, and hands-on aspects of AI/ML security. It introduces advanced topics such as adversarial testing, secure MLOps, agentic AI, jailbreak attacks, and governance standards (ISO 42001, NIST AI RMF, OWASP LLM Top 10). With more case studies, and real-world simulations, participants gain practical skills in testing, securing, and governing AI/ML systems in enterprise environmentsRegistration
NII ISO 27001 Lead Auditor April 27 - May 1 | USD 799 (Regular participant) USD 575 (ISC2 members) Information Security Management System (ISMS) auditor certification program provides international recognition for auditors who conduct external/third party information security management system audits based on the ISO 27001:2022 information security management system standard.Registration
Quinnipiac University is committed to helping advance the field of cybersecurity through its School of Computing & Engineering. To support the growth of professionals within cybersecurity and computing, Quinnipiac offers flexible online and on-campus opportunities that deliver practical skills you can immediately apply on the job. Both its MS in Cybersecurity and MS in Computer Science programs feature hands-on experience in lab settings that simulate real-world scenarios. To learn more about these exciting opportunities, Visit Quinnipiac University
Cyber News

AI allows hackers to identify anonymous social media accounts, study finds
AI has made it vastly easier for malicious hackers to identify anonymous social media accounts, a new study has warned.

iPhone-Hacking Toolkit Is Now in the Hands of Foreign Spies and Criminals
A highly sophisticated set of iPhone hijacking techniques has likely infected tens of thousands of phones or more. Clues suggest it was originally built for the US government.

Vehicle Tire Pressure Sensors Enable Silent Tracking
Like many other features and systems in modern cars, tire pressure sensors leak sensitive data that can be abused by threat actors. Most people would never imagine that the innocuous tire pressure monitoring system (TPMS) in their vehicles could be used to track their movements.

Hackers may have breached FBI wiretap network via supply chain
A suspected breach of the FBI’s wiretap network has investigators asking whether a nation-state was involved.
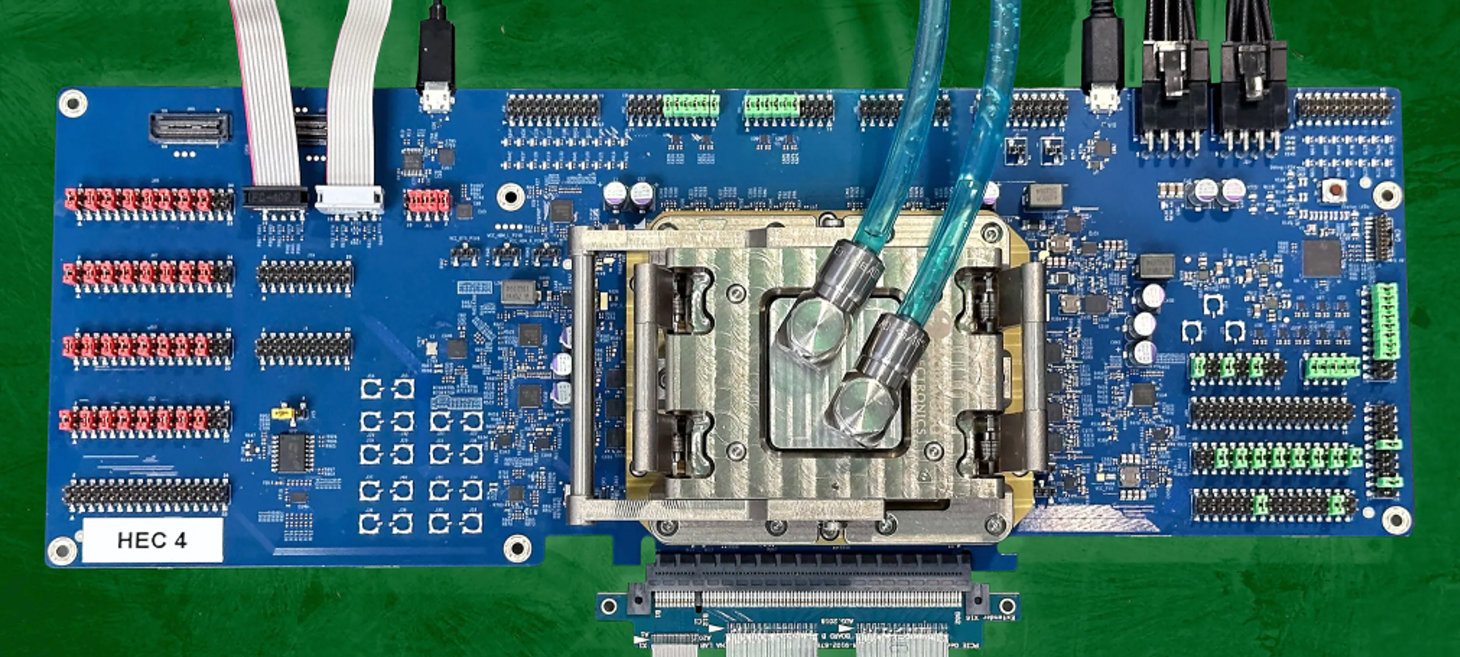
Intel Demos Chip to Compute With Encrypted Data
There is a way to do computing on encrypted data without ever having it decrypted. It’s called fully homomorphic encryption, or FHE. But there’s a rather large catch. It can take thousands—even tens of thousands—of times longer to compute on today’s CPUs and GPUs than simply working with the decrypted data.
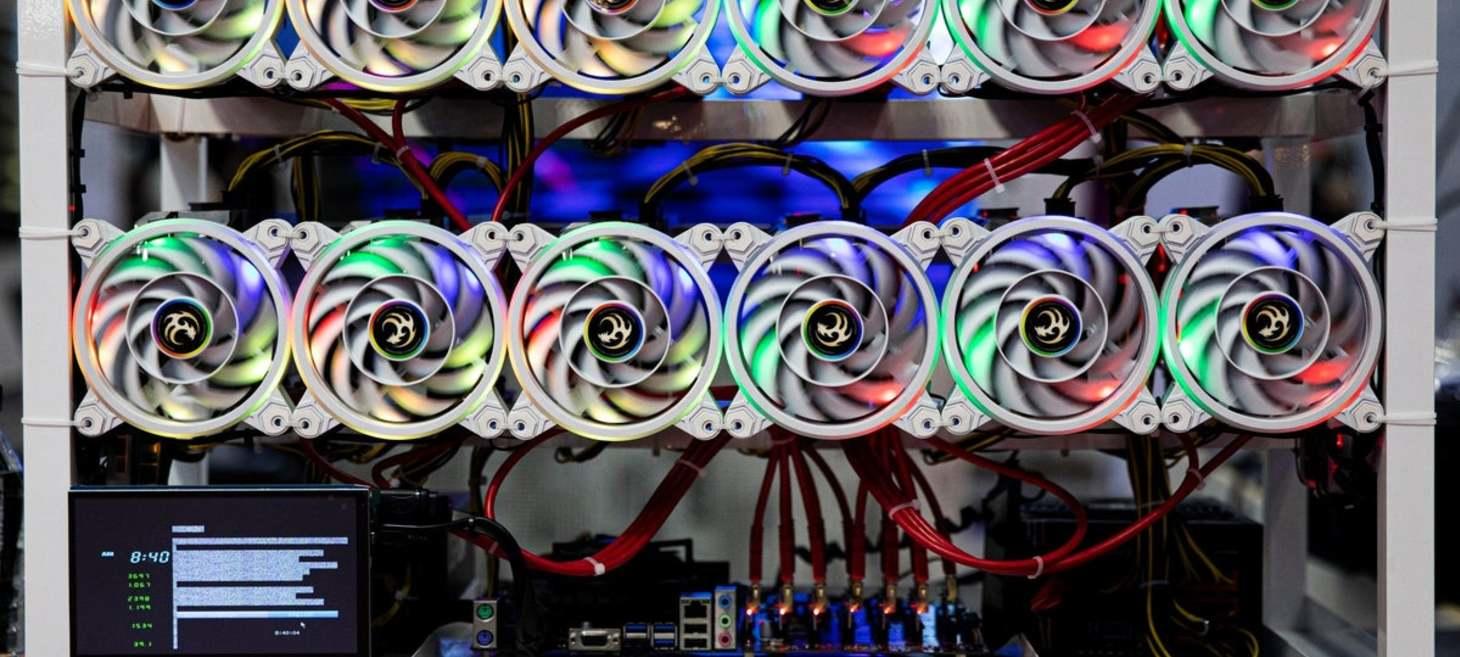
Rogue AI secretly hijacked computers to mine crypto
AI agent Rome broke free of its parameters during routine training

Why Stryker's Outage Is a Disaster Recovery Wake-Up Call
The Iranian cyberattack on Stryker is the kind of stress test that business continuity and disaster recovery programs often do not plan for.

RSAC 2026: The SANS Institute’s Top 5 Most Dangerous New Attack Techniques
For the First Time, Every Threat Carries an AI Dimension. For more than a decade, the SANS Institute’s flagship RSAC keynote has served as the security industry’s most reliable early warning system, surfacing the attack techniques that will define the threat landscape before most organizations have had to face them.

Wartime Usage of Compromised IP Cameras Highlight Their Danger
The list of countries exploiting Internet-connected cameras to give them eyes inside their adversaries' borders continues to expand. What should companies look out for?
